- Home
- Programs
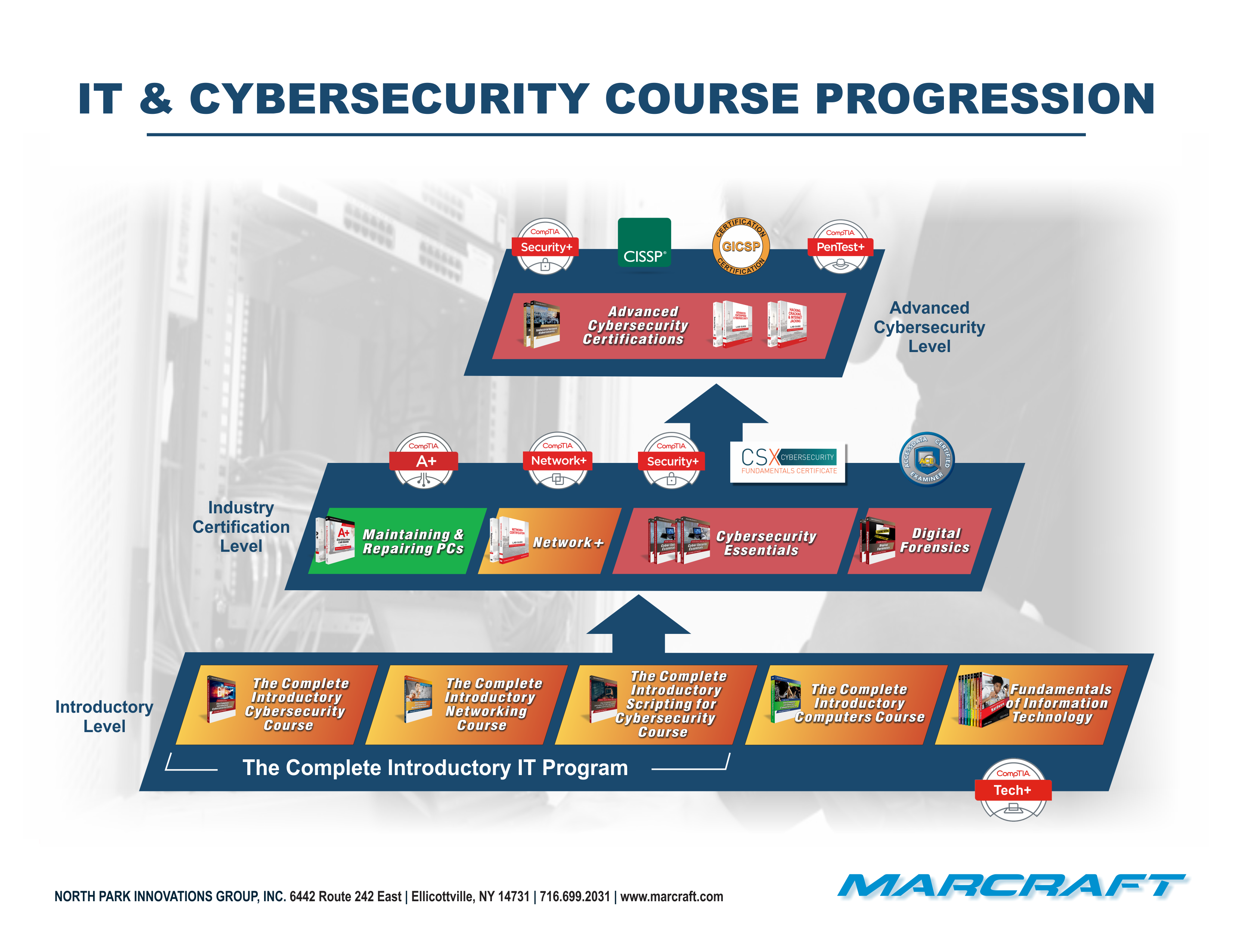
- IT & Cybersecurity Programs
- MC-1100 Tech+
- MC-2300 Introduction to Computers
- MC-2400 Introduction to Networking
- MC-2500 Introduction to Cybersecurity
- MC-3500COM Introduction to Networking & Cybersecurity Combo
- MC-2600 Introduction to Scripting for Cybersecurity
- MC-9000 Maintaining & Repairing PCs Certification Program
- MC-4000, MC-4001, & MC-4002 Network+ Certification Program
- DF-1000 Digital Forensics
- CS-1000 Cybersecurity Essentials
- CS-2000 Advanced Enterprise Cybersecurity
- CS-3000 Industrial Networks Cybersecurity
- CS-4000 Cybersecurity Analyst
- CS-5000 Certified Pentester
- Green Technology Programs
- GT-1500 Generating Clean Electrons
- GT-2500 Sustainable Conservation
- GT-1000 Solar Photovoltaic Installer Certification Program
- GT-2000 Wind Turbine Installer Certification Program
- GT-9500 Solar/Wind Energy Certification Program
- GT-3000 Fuel Cell Training Program
- GT-5000 Hydropower Training Program
- GT-6000 Biofuels Training Program
- GT-7500 Energy Auditing Certification Program
- GT-900T Green Technology Concepts and Practices Textbook
- SCADA Add-Ons for Green Technology
- Drones (Uncrewed Aircraft)
- OTHER PROGRAMS
- STS-1000 STS Basic Certification
- STS-6000 STS Audio/Video Endorsement
- STS-8000 STS Computer Networking Endorsement
- STS-8500 STS Environmental Control Endorsement
- STS-9000 STS Security & Surveillance Endorsement
- DC-6000 Fiber Optic Installer Certification Course
- DC-2000 Commercial Low-Voltage Wiring Certification Program
- SS-2000 Security & Surveillance Certification Program
- TERRA
- IT & Cybersecurity Programs
- Certification
- News
- Videos
- Funding Resources
- Contact Us!